Understanding the Intricacies of Ransomware
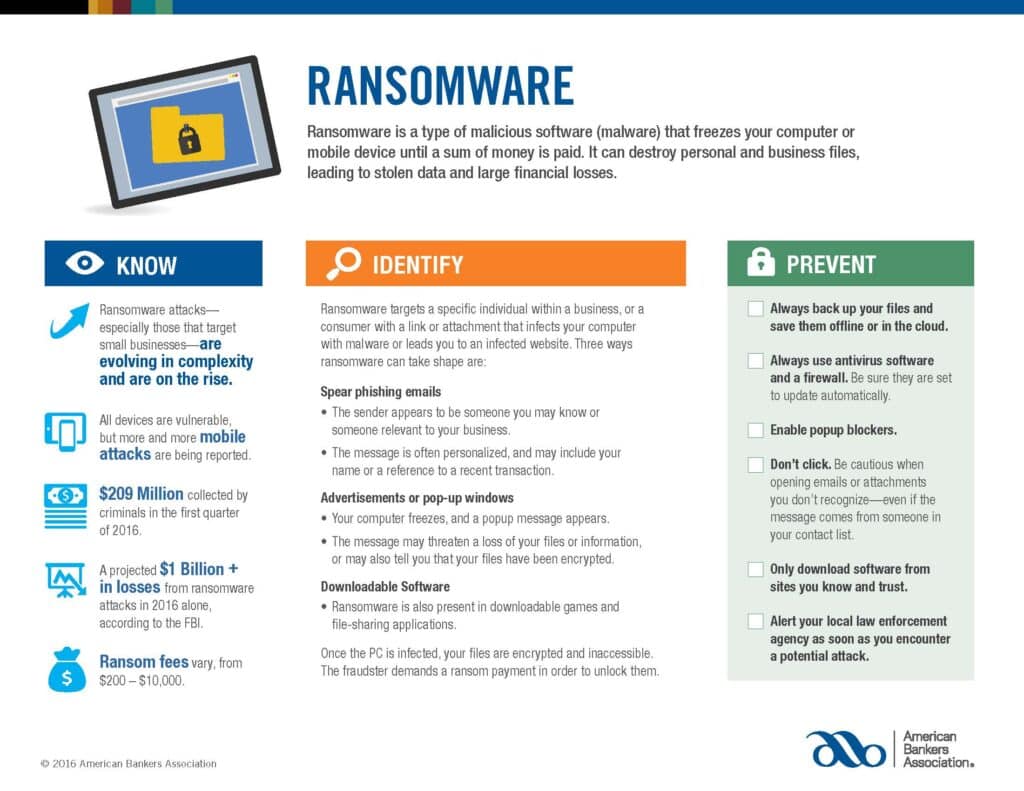
Ransomware is malicious software, commonly referred to as malware, that takes your computer or mobile device hostage until you pay a designated sum of money to the perpetrators. It’s more than just a simple lockout from your system; ransomware can permanently destroy both personal and business files, leading to theft of sensitive data and substantial financial losses. What’s particularly alarming is how ransomware attacks are growing in complexity, becoming more difficult for individuals and organizations to defend against.
The Financial Impact and Growth Trajectory
The financial implications of ransomware are staggering. According to FBI statistics, criminals amassed approximately $209 million in the first quarter of 2016 alone. This was a precursor to an even more alarming figure: losses from ransomware attacks for the entirety of 2016 were projected to exceed $1 billion.
The ransom fees vary widely, ranging from as little as $200 to a staggering $10,000 or more, depending on the vulnerability and the importance of the targeted data. This is especially relevant for small businesses, as they are increasingly becoming a target of such attacks.
Device Vulnerability: From Computers to Mobile Devices
While it may be a common misconception that only computers are susceptible to ransomware, mobile devices increasingly fall victim to these types of attacks. This expanding threat landscape highlights the urgency for businesses and individuals alike to adopt robust cybersecurity measures across all kinds of hardware.
Identifying the Mechanisms of Ransomware Attacks
Ransomware does not operate in a vacuum; it’s often delivered via sophisticated tactics tailored to deceive the target. Typically, ransomware targets either a specific individual within a business or a consumer, luring them into clicking a malicious link or attachment that initiates the malware infection. There are three main methods through which ransomware is commonly delivered:
- Spear Phishing Emails: These targeted emails appear to come from someone the recipient knows or someone relevant to their business, like a client or a vendor. The content of the email is often personalized, including the recipient’s name and possibly references to recent transactions or shared interests. For small businesses, an email appearing to be from a trusted financial institution could be a potential trap.
- Advertisements or Popup Windows: Another way ransomware infects a system is through malicious advertisements or popup windows. In these instances, the computer suddenly freezes, and a popup appears, often threatening the loss of files or stating that the files have already been encrypted.
- Downloadable Software: Ransomware can also lurk in seemingly innocuous downloadable games or file-sharing applications. Once downloaded and activated, the ransomware goes to work encrypting your files, making them inaccessible until a ransom is paid.
Best Practices for Prevention
For businesses and individuals, prevention is undoubtedly better than cure regarding ransomware attacks. Here are some crucial steps you can take:
- Robust Backup Strategy: Always make sure to back up your essential files. These backups should be stored offline or in a secure cloud storage facility to protect them from ransomware attacks.
- Cybersecurity Infrastructure: Utilize antivirus software and a robust firewall. Ensure that these tools are set up to update automatically, as cyber threats are constantly evolving.
- Popup Blockers and Safe Browsing: Enable popup blockers on your browsers, and exercise caution when clicking on advertisements. Always be cautious when opening emails or attachments from sources you don’t recognize—even if they appear to be from someone you know.
- Trusted Software Sources: Only download software and applications from websites that you know and trust. Companies should enforce strict software download and installation policies.
Immediate Reporting
Should you suspect a ransomware attack, it’s imperative to alert your local law enforcement agency immediately to mitigate damage and possibly catch the perpetrators.
As the ransomware threat continues to rise, both in complexity and frequency, individuals and organizations must stay vigilant and proactive in their cybersecurity efforts.
If you are a Legacy client and have questions, please do not hesitate to contact your Legacy advisor. If you are not a Legacy client and are interested in learning more about our approach to personalized wealth management, please contact us at 920.967.5020 or connect@lptrust.com.
This newsletter is provided for informational purposes only.
It is not intended as legal, accounting, or financial planning advice.