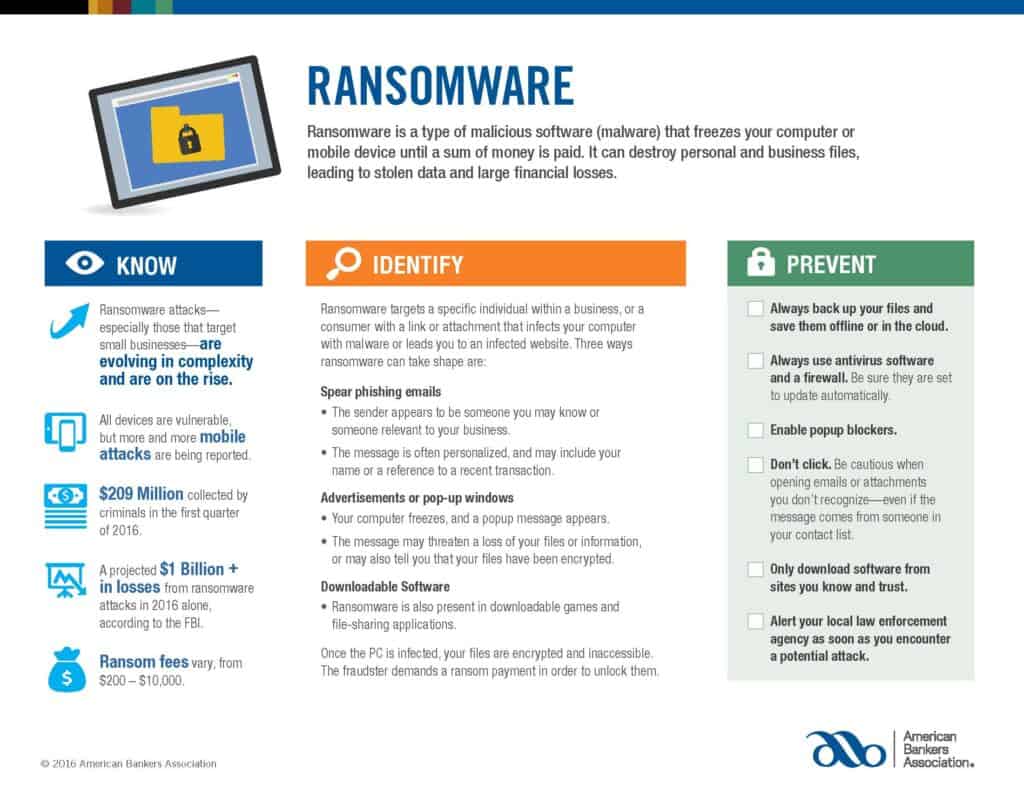
In an increasingly digital world, the risk of cyber threats has become unavoidable for businesses of all sizes. Among these dangers, ransomware attacks have emerged as particularly destructive, capable of paralyzing operations and compromising sensitive data. This article highlights the importance of a well-articulated plan for dealing with potential ransomware attacks. By understanding how to mitigate damage, accurately assess the impact, and prepare a comprehensive response strategy, business owners can transform their approach to such threats from reactive to proactive. Explore the MAP (Mitigate, Assess, Prepare) guide the American Bankers Association provides for responding to ransomware attacks and learn how to safeguard your business from these debilitating cyber onslaughts effectively.
Mitigate Damage
- Isolate the affected device(s): Determine which systems are infected. Temporarily take the network offline if possible. Disconnect all infected or potentially infected components from the network to contain the spread.
- Do not erase or attempt to fix corrupted files: This could disrupt the “crime scene” and hinder investigative and recovery efforts.
- Do not power down the device: Ransomware artifacts and evidence could be lost if components are completely powered down. Virus spread vs. evidence retention should be weighed by senior leadership. If unable to disconnect devices from the network, power them down to contain the infection.
Assess Damage
- Triage systems for restoration and recovery: First, identify and prioritize critical systems for recovery. Image system and affected devices. Collect all relevant logs or indicators of compromise (e.g., suspicious commands) and preserve them for analysis.
- Evaluate whether backup data is available: Ensure backups are not connected to the corrupted system. To limit the chances of reinfection, consider restoring data from the oldest version of a backup, preferably older than 100 days.
Prepare Response
- Engage law enforcement in consultation with your legal department: Contact the FBI and Secret Service. Law enforcement may provide intelligence that could decrypt your systems. They may also assist in navigating regulatory reporting requirements.
- Decide whether to pay the ransom: In consultation with senior leadership, the legal department, your insurance provider, and other stakeholders, decide whether to pay.
- Determine whether to hire or consult with an external forensic group to assist in recovery, potential payment, and further mitigation.
- Notify customers and appropriate federal and state bodies: Contact the appropriate regulatory bodies about customer data breaches. Follow your state’s data breach notification requirements.
Ransomware, a pernicious type of malware that holds data hostage in exchange for payment, is one of the most daunting cyber threats businesses face today. The scale of disruption and potential damage inflicted by such attacks underscores the necessity of comprehensive preparation. By understanding and implementing the MAP (Mitigate, Assess, Prepare) strategy, businesses can use the tools to counter these cyber onslaughts proactively rather than reactively. As we conclude this discussion, we strongly encourage you to view the accompanying infographic below. This visual guide serves as a succinct and handy reference, further delineating how to manage the ransomware threat and fortify your business’s digital defenses.
If you are a Legacy client and have questions, please do not hesitate to contact your Legacy advisor. If you are not a Legacy client and are interested in learning more about our approach to personalized wealth management, please contact us at 920.967.5020 or connect@lptrust.com.
This newsletter is provided for informational purposes only.
It is not intended as legal, accounting, or financial planning advice.